What is cybersecurity and why is it important/types/working/Role
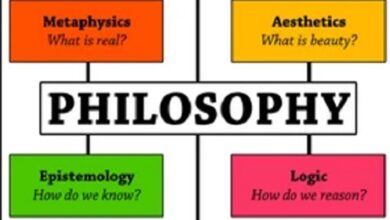
What Is Cybersecurity?
Cybersecurity is a set of actions and techniques to protect systems , programs, networks and equipment from intrusion.
In this way, it is possible to ensure that valuable data is not leaked or compromised in cyber-attacks .
These attacks may be intended to access servers, steal passwords, hijack data, or even defraud financial transactions.
Often, however, cybersecurity is confused with information security practices .
How Does Cybersecurity Work?
There are more than 439,000 intrusion attempts and distributed denial-of-service (DDoS) attacks registered, which leaves us only behind the United States in this ranking.
For this, they need to prepare an entire plan, which includes a specific budget for the IT area, in order to define policies and data security measures.
Among the possible actions to be taken, the following stand out:
- Automated penetration testing with vulnerability analysis
- Implementation of centralized security platforms to control, monitor and neutralize threats on the network, endpoints and distraction of possible attackers
- Protection for Bluetooth and Wi-Fi devices
- Shielding Confidential Data .
How Important Is Cybersecurity?
Companies suffer at least one cyberattack per year , as pointed out by the BugHunt National Research on Information Security .
As the popular saying goes: “opportunity makes the thief”.
That is, if there are intruders, it is because there are security flaws that allow them to act freely.
The only possible response to contain this threat is to invest in cybersecurity and information security measures, in an attempt to avoid financial losses caused by attacks.
What Are The Types Of Cybersecurity?
Generally, cybersecurity is every measure by which individuals and companies are able to protect their devices and files from the threat of malicious hackers.
In fact, it should be noted that the term hacker, in itself, does not designate a criminal, so much so that some people use the term cracker to refer to those who practice virtual crimes.
Just as there are different types of hackers, there are also different types of cybersecurity .
Each of them applies to a certain type of equipment, data traffic stage or environment, among other possibilities.
Shall we meet some of them below?
Operational Security
Imagine that you are a newly hired employee of a startup with great reputation in the market.
In this case, you should certainly not have access to restricted company data, such as those related to accounting and tax, for example.
This type of control is part of the operational security routines , in which the company decides how it will protect its data, defining who accesses it and how they access it.
By the way, companies that fail in this aspect expose themselves to so-called insiders , as hackers who act within their facilities are known, taking advantage of privileged access.
Network Security
DoS (Denial Of Service) and DDoS attacks are among the most common.
They consist of artificially overloading the flow of data on a network , making its use unfeasible by its users.
Let’s say, for example, that a cracker intends to steal sensitive data from a company, but, for that, he needs, at the same time, to prevent the IT area from trying to contain him.
A DDoS, in this case, can serve as a “ smoke screen ”, by blocking people from accessing the network where the attacked servers are located.
Containing this type of attack is one of the functions of professionals and sectors intended to provide network security, which also includes protection against malware in general.
Application Security
Just as networks are exposed to attacks, so are the applications we use, whether in a personal context or within companies.
Application security is cybersecurity’s response to threats directed to software installed on computers and mobile devices in general.
In this way, sensitive data, especially passwords and access data, are protected.
For this, companies that provide applications define the security protocols to be implemented even before starting to develop them.
End User Education
A cyberattack is not always the result of the deliberate action of a cracker or an insider.
There are cases where viruses and malware are inadvertently distributed by ordinary users who unknowingly repeat risky behavior.
To prevent this type of spread of malicious agents, companies that invest in cybersecurity must also focus on end-user education.
In this regard, they take responsibility for carrying forward cybersecurity information, warning about the risks of opening certain types of email and connecting USB devices.
In this way, it is possible to mitigate the high unpredictability generated by the lack of knowledge that the average person has about online security.
Cloud Security
Like network security, cloud security is dedicated to anticipating threats that surround a set of devices that share access to platforms in that environment.
It aims to prevent unauthorized data leakage, in addition to shielding the cloud against possible weaknesses and susceptibilities.
It also seeks to exploit possible weaknesses in access controls, in order to avoid attacks and interruptions in the availability of cloud computing services.
In the case of cloud systems, the main threats are malware and attacks, such as so-called advanced persistent threats (APTs).
Cybersecurity Vs Information Security: The Differences
Cybersecurity is actually a part of information security .
Does it look confused? Let’s explain!
The Role Of Cybersecurity
Cybersecurity is focused on software, hardware and networks .
That is, it takes care that the company’s system does not allow cyber attacks.
It prevents problems with the management of information that is done by the machines, in the transit and storage of data between them.
This way, it protects the digital information stored there.
For this, some of the measures taken are: applying antivirus on the machines, having backup copies of what is on the servers, encrypting data and offering digital signature technology.
It is what makes it more difficult to lose information permanently and also prevents possible fraud, for example.
What Is Information Security?
Information security, on the other hand, is a little more comprehensive.
She cares about protecting all company data .
That is, we are talking from the physical storage of information to the data that is managed by people.
As a result, activities to ensure information security are varied.
They go through rules for transporting computers and work equipment, remote access to the company’s network, password change policy , ensuring that employees are using strong passwords and even manuals on what information can be given to which people.
Cybersecurity In The World
Globally speaking, the numbers related to cybersecurity are better than on the national scene, but they are still scary.
Nearly 690 million people in 21 countries studied (about 31% of internet users in this sample) were affected by cybercrime.
The financial loss because of this was about $125 billion in just one year.
The World Economic Forum also brought the issue to the agenda and this type of crime was rated as the sixth largest in impact.
These attacks are expected to cost companies worldwide up to $8 trillion over the next 5 years.
Despite this, there is an ongoing movement on the part of companies and countries to take cybersecurity issues more seriously.
One of the signs of this concern is the increase in CISO positions in large companies.
The CISO (Chief Information Security Officer) is responsible for defining data control standards, implementing maintenance processes and deciding which strategies will be used to contain attacks .
The US government itself has hired an executive for this position.
In addition, it also took measures to increase its information security spending by 35% , reaching US$ 1.9 billion in investments.
Europe is also not far behind when it comes to cybersecurity.
Countries in the bloc launched a law in 2018 to pressure their trading partners to protect data in transactions between companies.
The law, called the General Data Protection Regulation , obliges companies with customers in the European Union to report any recorded digital attack to data protection bodies within 72 hours.
If this is not complied with, fines can reach up to 20 million euros .
As we will see in the next topic, these moves are positive for anyone who is already or wants to become a cybersecurity professional.
After all, European pressure forces companies in other countries to react and protect themselves from cyber-attacks to remain internationally competitive.
Examples Of Threats Tackled By Cybersecurity
DDoS attacks, malware and APTs are just a few of the many types of cyberattacks that a person or network in a company can suffer.
The variety of threats, in fact, has justified the high investments that governments and private institutions have been making in cybersecurity.
After all, against a multifaceted enemy you don’t play around.
Sophisticated control measures must be adopted to make life as difficult as possible for potential invaders .
However, there are certain types of threats that are more frequent than others, considering the objectives for which they are proposed and the greater ease of carrying them out.
Discover four of them below.
Man-In-The-Middle Attack
Man-in-the-middle (MITM) attacks consist of the theft of confidential data by an attacker who intercepts a communication.
This is usually an attack aimed more at stealing bank details, but it can be targeted for any type of online transaction.
One of the ways cybercriminals who use MITM act is to send fake invoices to victims’ email addresses.
They can also take advantage of security holes in routers , creating a fake network that people connect to.
From there, they gain freedom to intercept all communications, gaining control over all information exchanged.
Malware
Perhaps the most recurrent of cyber threats are malware, software containing malicious instructions aimed at stealing information , among other fraudulent purposes.
In this type of cyber threat, the malicious hacker sends by email or even by messaging applications a link that, if clicked, leads to the installation of this program.
In e-mail, malware is sent in the form of attachments that, in turn, lead to .exe (executable) type applications.
For this reason, it is essential to have antivirus programs or extra protection in email accounts that can detect this form of threat, preventing its propagation.
Ransomware
Ransomware is a type of malware whose purpose is to block access to files and directories on a device.
In this way, the attackers charge a kind of “ransom” to return access to this data, thus configuring a crime of extortion.
The main risk, in this case, is the payment of the amount demanded by the criminal who, even so, does not return access to files locked by encryption.
This makes this virtual crime more recurrent among companies that, as such, would have more confidential data to protect and greater economic power to pay large sums to swindlers.
Phishing
While relatively easier to detect, phishing attempts can be quite convincing.
This is because, in this type of cyberattack, crackers pose as serious companies through emails requesting certain types of data.
This is what happens, for example, in messages falsely signed by banks, asking for passwords to be re-registered.
Phishing attacks also aim to steal data from credit cards or e-wallets such as Paypal.
What To Do To Ensure Cybersecurity In Companies?
Due to the immense damage that can be caused by virtual attacks, there is little care when it comes to cybersecurity.
In this sense, together with the sector or an IT specialist, it is essential to adopt preventive measures to avoid leakage of sensitive data and its sources .
Check it out below:
- Perform backups regularly !!!
- Have access control mechanisms
- Invest in a professional antivirus solution
- Define your internal security policy
- Have a shielded connection
- Use digital signatures
- Monitor systems and networks
- Promote training for IT teams.
The Importance Of Cybersecurity In Industry 4.0
In a context in which all production processes are digital or scannable, cybersecurity gains even more relevance .
Companies tend to structure their processes more and more online, as advocated by the principles of the so-called industry 4.0 .
In it, the internet, cloud computing and concepts such as the Internet of Things (IoT) and Bring Your Own Device (BYOD), among others, guide the decisions and the way of producing companies.
Therefore, it is essential to invest in systems capable of anticipating virtual threats and, at the same time, define protocols and policies to avoid exposure to them.
Top Cybersecurity Trends For The Coming Years
Considering what the statistics say and what the market itself suggests, it is possible to point out trends in cybersecurity that should consolidate in the near future .
Are they:
- Solutions based on Artificial Intelligence (AI)
- Greater presence of Compliance specialists
- Cyberattacks on healthcare companies and ransomware-type
- zero-day attacks
- Sophistication of phishing attacks
- Invasions seeking financial data.
Future Professions And Cybersecurity
We can say that even now, in the present, data is the king of any decision making in a company .
It is not by chance that the expression big data has been increasingly associated with assertive work with the target audience of each company.
In addition, companies in around the world) are investing more in cloud computing .
And, of course, where there is information traveling and servers being activated, the cybersecurity professional is very necessary.
The first step in becoming one is to invest in a degree in Information Technology .
However, cybersecurity is one of several areas within IT.
Soon, you will have to specialize and take additional courses.
For this, seek to delve into the universe of security in hardware , search for courses on blockchain , cryptography, cloud security and formation of secure networks.
It is also worth studying more about cybersecurity for cell phones, as these devices are responsible for a large part of digital fraud , especially through malicious apps.
The important thing is to keep up to date with the technologies that are emerging all the time for data protection.
What Are The Main Responsibilities Of A Cybersecurity Professional?
Like other security professionals , the specialist in this area has the main role of protecting companies from cyber threats .
Cybersecurity professionals are also responsible for:
- Detect, analyze and qualify any incidents
- Manage the activities of a Security Operational Center (COS)
- Guide teams on control measures to be adopted in real cases
- Identify sources of potential attacks
- Supervise the application and operation of cybersecurity policies
- Record information of interest in order to expand knowledge about threat points and protective measures
- Non-stop monitoring for hardware and software vulnerabilities.
Types Of Jobs And Professions Related To Cybersecurity
As we have just seen, cybersecurity features prominently among the professions of the future .
But what are the positions related to this area?
In a quick search, you will find market mentions of positions such as cybersecurity analyst, cybersecurity engineer and cybersecurity consultant.
It is also worth remembering the position of CISO (Chief Information Security Officer), a trend outside the country, but which should soon appear prominently in companies.
There are also vacancies related to information security , which, as we highlighted before, tend to be more comprehensive, but also address cybersecurity.
Examples Of Cybersecurity Companies
Professionals who already have the necessary training or want to specialize in cybersecurity should be aware of the markets.
This means evaluating opportunities and also getting to know the companies that are reference in this area of activity.
To help you in this mission, we have separated information about two market giants.
These are examples of cybersecurity companies that can inspire you in your career .
ESET
ESET is a center of excellence in technological security that set out to build what must be, according to the company, the largest cybersecurity office in the world , in Bratislava, the capital of Slovakia.
Among the construction features, we highlight the 25 thousand square meters of offices and the forecast to house up to 1,400 employees (800 more than the current offices).
Thus, the best professionals in the field will be able to concentrate in the same place, providing cybersecurity solutions for other companies.
Chronicle
Chronicle is a sister company of Google .
It was launched in early 2018, a time when many US companies were suffering digital attacks.
One of them, for example, was Sony, which had its social networks taken and the data of PlayStation players leaked.
To deal with this problem, Chronicle offers surveillance on the cybersecurity level of companies , in addition to a powerful antivirus service for individual internet users.
Using machine learning to improve its process, Chronicle entered the market on the right foot.
Currently, it has been testing its products in some of the 500 largest companies in the world, according to Fortune Magazine.
5 Reasons To Specialize In A Cybersecurity Career
Interested in the area? Or are you still in doubt whether to follow this career?
Here are five reasons you should invest in cybersecurity for your professional future .
1. There Are A Lot Of Vacancies In Cybersecurity
While certain occupations suffer from unemployment, those choosing cybersecurity are on the rise.
Another useful information for anyone thinking of specializing in this area is that there is a lack of skilled labor to take on the positions offered.
Cybersecurity Nexus claims that 59% of cybersecurity organizations in the world have 5 candidates vying for each vacancy – well below the average for other professions.
Finally, it is worth checking the data from the Cybersecurity Workforce Study , which found that there were more than 3 million cybersecurity professionals in the world.
In Latin America alone, the shortage of professionals reaches 136,000 positions.
2. You Will Have Chances To Work All Over The World
As we mentioned above, there is a lack of specialized professionals to take on cybersecurity positions, even in more developed countries , where this practice is already more common and investments are greater.
If working abroad is a goal, it is worth investing in a good English course and practicing the language.
Not to mention the specialization in the area itself, of course.
With the shortage of cybersecurity professionals in the market, you will have a good chance of getting the much-desired position.
3. Cybersecurity Salaries Are Worth It
The supply of vacancies greater than the demand for good professionals encourages high remuneration in the market.
Not to mention salaries paid in dollars or euros, which is the case for those who choose a company outside.
According to the consultancy Robert Half , the earnings of a cybersecurity analyst, which is the starting point of a career in the area, were around R$3,000 per month.
A cybersecurity manager, on the other hand, can count on salaries above R$20,000 .
4. It’s A Growing Area
When we talk about cybersecurity, we are referring to a market in which policies still need to be decided and established, both for companies and governments.
That is, it is still in an embryonic stage , but with great growth expectations.
In large part, this is justified because the number of digital attacks increases worldwide.
One of the most famous cases was that of a virus called WannaCry , a type of ransomware (ransom virus) that hijacked data on more than 300,000 computers in 150 countries.
Companies are also progressively more dependent on their internal systems to function.
Combining all these factors, what emerges is the scenario of a future that will demand more and more cybersecurity professionals in companies.
Its role will be to ensure that data is kept and protected, no matter what threat appears or from which country it is being accessed.
5. You Will Be Constantly Evolving
For those who like the idea of working on something they love and don’t want to spend the rest of their lives doing the same thing, cybersecurity is a good way to go.
After all, systems are constantly evolving and new digital crimes appear every day .
In other words, the challenges will be constant.
Therefore, the ideal is for the professional in this area to be someone who is frequently updated, creative in solutions, tireless to deal with problems and attentive to details to avoid any failure in the system.
The Best Cybersecurity Books
If you are interested in delving even further into the vast field of cybersecurity, you can turn to the main publications on the subject.
Check it out below:
- Countdown to Zero Day (Kim Zetter)
- Ghost in the Wires: My Adventures as the World’s Most Wanted Hacker (Kevin Mitnick)
- Applied Cyber Security and the Smart Grid: Implementing Security Controls Into the Modern Power Infrastructure (Raj Samani)
- The Cuckoo’s Egg (Clifford Stoll)
- Cyber Warfare: The Next Security Threat and What to Do About It (Richard A. Clarke)
- Digital Resilience: Is Your Company Ready for the Next Cyber Threat? (Ray A. Rothrock).